-
Vorsicht, wenn die Polizei anruft. Dahinter könnten Betrüger stecken, die es auf Ihr Geld abgesehen haben. Bild: Andreas/fotolia.com Wer unerwartet einen Anruf von der Polizei bekommt, sollte vorsichtig sein. [Mehr]
-
Wer aktuell eine SMS erhält, die angeblich von einem Paketdienst stammt, sollte äußerst vorsichtig sein. Denn der Link in dieser SMS führt zur Installation eines gefährlichen Programms auf dem Smartphone. [Mehr]
-
 Aktuelle Warnungen
Aktuelle WarnungenWenn die Polizei anruft und vor Einbruch warnt: Vorsicht vor Telefonbetrügern
-
 Aktuelle Warnungen
Aktuelle WarnungenErpresser-Mail droht mit CIA-Ermittlungen wegen Kinderpornos
-
 Datenschutz und Anonymität
Datenschutz und AnonymitätNach EuGH-Urteil: Facebook-Fanpage schließen oder nicht?
-
 Recht
RechtDSGVO: Erste Abmahn-Anwälte sind schon aktiv
-
 Sicherheit im Internet
Sicherheit im InternetBis 31. Mai: Western Union erstattet Betrugsopfern Geld zurück
-
 Recht
RechtNetzagentur: Beschwerden über Lockanrufe stark gesunken
Aktuelle Warnungen
-
Vorsicht, wenn die Polizei anruft. Dahinter könnten Betrüger stecken, die es auf Ihr Geld abgesehen haben. Bild: Andreas/fotolia.com Wer unerwartet einen Anruf von der Polizei bekommt, sollte vorsichtig sein. [Mehr]
Abofallen im Internet
-
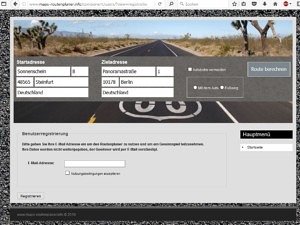
Schon seit Monaten locken falsche Routenplaner im Internet unter wechselnden Adressen Verbraucher in eine Kostenfalle. Die Suchmaschine Bing dient den Abzockern dabei als Verbreiter. maps-routenplaner.info: Abofalle [Mehr]
TIpps und Hilfe
-
Symbolbild: Grecaud [Mehr]
2021 Computerbetrug.de - alle Rechte vorbehalten